Extract Fields with vRealize Log Insight
- Brock Peterson

- Apr 24, 2022
- 2 min read
VMware vRealize Log Insight (vRLI) is a powerful logging tool with all sorts of capabilities, one of them being the ability to extract fields from log entries.
Out of the box, each vRLI log entry will contain certain fields like source, event_type, file path, hostname, and more. They are documented here.

Beyond those, there are Extracted Fields, which are user defined or Content Pack defined fields extracted from log entries. For example, the VMware vSphere Content Pack comes with dozens of Extracted Fields as defined here.

Another example might be the Extracted Fields in the Oracle Database Content Pack.

I use Extracted Fields in Queries, Dashboards, and Alerts. There are times when I need to create an Extracted Field of my own. Say for example, we start collecting F5 BIG-IP logs and want to know about Certificate Expirations. The logs are rich, but they don't have the Certificate Name field or the Certificate File field defined.

Here are some F5 BIG-IP logs that show expired and expiring Certificates. I'd like to extract the Certificate and the Certificate File location to be used in email notifications. How do we do it?

Highlight the field you want to extract from the log entry and click Extract field.
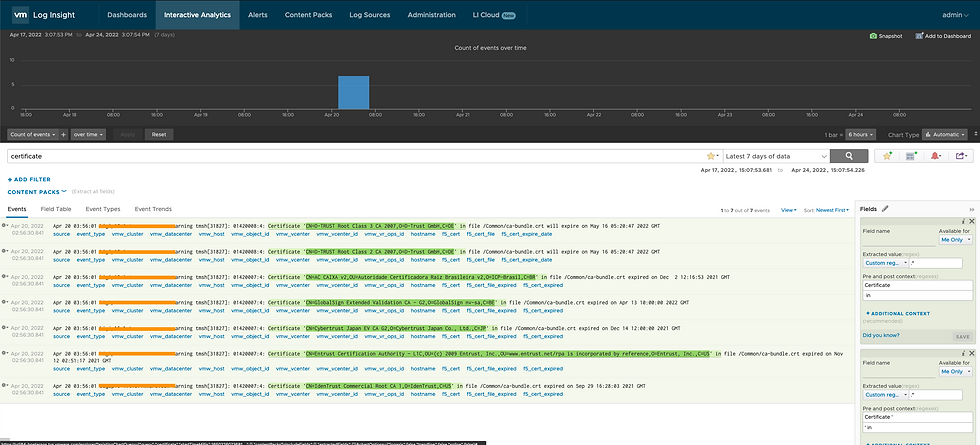
That field will be highlighted in all entries, this will help you confirm you are extracting what you want. In the right pane you have the ability to customize your Extracted Field: give it a name, share it, define pre and post context, customize REGEX, and more. Here you can see a Query with Extracted Fields.

I've defined several:
f5_cert - Certificate expired or expiring
f5_cert_file - location of Certificate
f5_cert_expire_date - date on which Certificate will expire
f5_cert_expired_date - date on which Certificate expired
We can now use any of these in Queries, Dashboards, or Alerts. Say for example, you want the Alert for Expired Certificates to include the Certificate itself, your email might look something like this.

Remember that only one static or extracted field is supported in emails from vRLI, documentation can be found here. For more information and a trial on vRLI go here!
Comments