Windows Events with VMware vRealize Log Insight
- Brock Peterson

- May 23, 2021
- 2 min read
Updated: Apr 27, 2022
I'd like to know which Windows Servers in my environment have seen EventID 4740 in their Security Log, indicating a user account has been locked. How can I efficiently scan the Security Logs on thousands of servers? Well, the short answer is vRealize Log Insight (vRLI), let's do it!
We'll need vRLI Agents on the Windows Servers, vRLI supports everything from Windows 7 to Windows 2019, the documented list of supported platforms can be found here: https://docs.vmware.com/en/vRealize-Log-Insight/8.4/com.vmware.log-insight.agent.admin.doc/GUID-83976956-C16C-42BD-9950-C6EDDF983086.html
There are several ways to install vRLI agents (vSphere Templates, vRA Cloud Templates, vRO Workflows, NFS Shares, vRA SaltStack Config, locally, etc). For the purposes of this blog, we'll install them locally.
The vRLI Agent package can be found on the vRLI appliance itself under Administration - Management - Agents.

Click the Download Log Insight Agent link.

Once downloaded, the Windows MSI can be run. Note that the download is self-aware, so once installed it'll automatically point itself at the vRLI appliance it was downloaded from. I've downloaded the package to the Windows Server 2012 R2 and started the install.

Accept the License Agreement and click Next.

Notice the vRLI Host is already configured. Click Install and you're done.

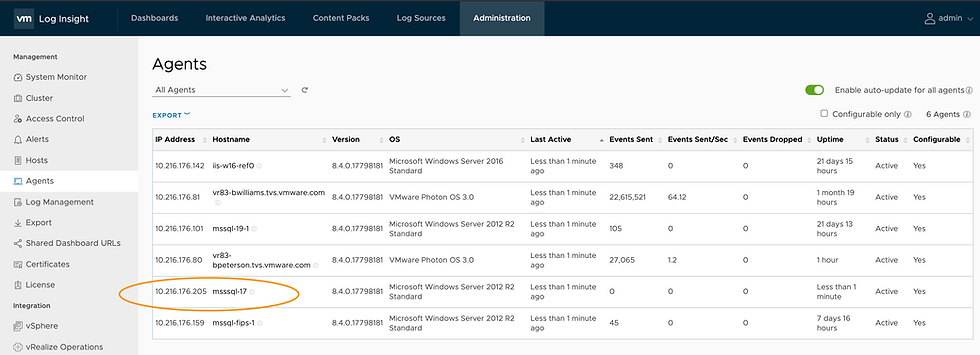
Back to vRLI, go to Administration - Management - Agents and you'll notice that the Agent has logged in.
Now that we have our Agents installed, let's configure them to capture the logs we want. We do this via Agent Configuration on the Administration - Management - Agents page.

I've selected Windows Agents in the dropdown at the top. Agent Configuration gives us the ability to tell the vRLI Agents what to capture.

We're going to focus on capturing Windows Events Logs, but there are six other powerful ways to capture Windows logs: Servers, General, Common, File Logs, Journal Logs, and Parsers. Documentation around vRLI Windows Agent configurations can be found here: https://docs.vmware.com/en/vRealize-Log-Insight/8.4/com.vmware.log-insight.agent.admin.doc/GUID-280BD438-9526-4C66-A6B7-AAC60E8587C2.html
Create a new Windows Event Log config by hovering over Windows Event Log, click NEW and follow the prompts. I've called mine WindowsSecurityLog.
You now have your configuration template.

Notice that the Windows Event Log Channel cannot be left empty, you have to point it at the Channel you want to capture. Specifically, the full name of the Channel as shown in Windows Event Viewer.

In this case we want to capture all Security Logs, but you can select whatever you want. You also have the ability to tag logs, exclude fields, configure accept and deny lists, and more. I'd like to capture all EventIDs from the Security Log, my config looks like this. Once done click SAVE AGENT GROUP.

We are now capturing Security Logs from all of our Windows Servers!

Now that we have the logs we can explore the Windows EventIDs. There are several different ways to do this. First, you can search for them via Interactive Analytics using filters.

You can also build dashboards using Interactive Analytics queries and charts, something like this. Here I've used six different queries and various chart types to explore my Windows Security logs. If you like it, you can get the dashboard here: https://code.vmware.com/samples?id=7619







Comments